BETVND 🏅 Nhà Cái BETVND.CASA TOP#1 THỊ TRƯỜNG 2024
BETVND là một trong những nhà cung cấp dịch vụ cá cược trực tuyến hàng đầu, đem đến cho người chơi một trải nghiệm đa dạng và chất lượng. Với các trò chơi phổ biến như đá gà, tài xỉu, bắn cá, xổ số, và game bài, BETVND đảm bảo sự an toàn, minh bạch và uy tín. Hãy cùng khám phá thế giới cá cược phong phú và cơ hội giành chiến thắng tại BETVND!
Giới thiệu nền tảng cá cược BETVND
BETVND là một nền tảng cá cược trực tuyến hàng đầu, được biết đến với độ uy tín cao và sự đa dạng trong các loại hình cá cược. Với giao diện dễ sử dụng, hệ thống bảo mật mạnh mẽ và dịch vụ chăm sóc khách hàng chuyên nghiệp, BETVND luôn đặt lợi ích và sự an toàn của người chơi lên hàng đầu. Ngoài ra, BETVND cung cấp hàng loạt trò chơi và các dịch vụ cá cược từ đá gà, tài xỉu, bắn cá, đến thể thao, lô đề, và game bài, mang lại cho người chơi nhiều sự lựa chọn hấp dẫn.
Cổng game đồng hành cùng betvnd : win777, fb68, 999bet vin, fb68, n666, nohu90, iwin, gen88, 33win, pg88, banca30, app hitclub, a8bet, ab77, red88.

Thế giới game BETVND có gì?
Game BETVND sở hữu một kho trò chơi đa dạng, bao gồm từ các trò chơi dân gian đến các trò chơi hiện đại, tạo nên một thế giới giải trí phong phú. Người chơi có thể tìm thấy mọi thứ từ cá cược thể thao, xổ số, bắn cá, đến game bài và lô đề. Sự phong phú này giúp game BETVND trở thành điểm đến lý tưởng cho những ai yêu thích cá cược và giải trí trực tuyến.
Đá gà BETVND
Đá gà là một trong những trò chơi cá cược truyền thống hấp dẫn nhất tại game BETVND. Người chơi có thể tham gia đặt cược vào các trận đấu đá gà trực tiếp từ các trường gà nổi tiếng tại Philippines và Campuchia. Game BETVND cung cấp nhiều lựa chọn cá cược đa dạng, từ đặt cược theo chấp, cược tài xỉu, cho đến cược theo tỷ lệ kèo. Với chất lượng phát sóng trực tiếp sắc nét và minh bạch, người chơi sẽ cảm nhận được sự hồi hộp và kịch tính từ từng trận đấu.
Tài xỉu BETVND
Tài xỉu là một trong những trò chơi cá cược được yêu thích rộng rãi, không chỉ ở Việt Nam mà còn trên khắp thế giới. Game BETVND cung cấp phiên bản tài xỉu trực tuyến với luật chơi đơn giản và giao diện thân thiện, giúp người chơi dễ dàng tiếp cận và tham gia. Trò chơi này chủ yếu dựa vào sự may mắn, nhưng cũng cần một chút kỹ năng và chiến thuật để dự đoán kết quả. Game BETVND cung cấp nhiều bàn chơi với mức cược khác nhau, phù hợp cho cả người chơi mới và những tay cược lâu năm.
Bắn cá BETVND

Bắn cá là một trò chơi giải trí kết hợp yếu tố cá cược, rất được yêu thích tại game BETVND. Trò chơi này đòi hỏi người chơi có kỹ năng quan sát tốt, tốc độ và sự khéo léo để săn những con cá có giá trị cao. Game BETVND cung cấp nhiều phiên bản bắn cá khác nhau, với các cấp độ khó dễ và phần thưởng đa dạng. Đây là trò chơi không chỉ mang tính giải trí cao mà còn có thể mang lại những phần thưởng hấp dẫn nếu người chơi có kỹ năng tốt.
Xổ số BETVND
Game BETVND mang đến dịch vụ cá cược xổ số trực tuyến với đa dạng loại hình, bao gồm xổ số miền Bắc, miền Trung, miền Nam và các loại hình xổ số quốc tế hấp dẫn. Người chơi có thể đặt cược theo nhiều cách khác nhau, từ chọn số, lô xiên, đến đánh đề. Tỷ lệ trả thưởng tại game BETVND rất cạnh tranh, giúp người chơi có cơ hội thắng lớn. Việc đặt cược xổ số tại BETVND cũng rất đơn giản và minh bạch, đảm bảo mang lại trải nghiệm tốt nhất cho người tham gia.
Thể thao BETVND
Cá cược thể thao là một trong những dịch vụ nổi bật của game BETVND, với sự bao phủ rộng rãi các môn thể thao được yêu thích như bóng đá, bóng rổ, quần vợt, cầu lông và nhiều môn thể thao khác. Game BETVND cung cấp nhiều loại kèo khác nhau như kèo châu Á, kèo châu Âu, kèo tài xỉu, và kèo tỷ số.Nhờ vào hệ thống cập nhật thông tin liên tục và chính xác, người chơi có thể dễ dàng theo dõi và thực hiện các cược vào các trận đấu hiện tại hoặc sắp tới.
Lô đề BETVND
Lô đề là một hình thức cá cược phổ biến tại Việt Nam và được BETVND phát triển thành một sản phẩm cá cược trực tuyến đầy hấp dẫn. Với nhiều cách chơi như lô xiên, lô trượt, bạch thủ lô, người chơi có thể thử vận may và kỹ năng tính toán của mình để giành chiến thắng. Tỷ lệ trả thưởng tại game BETVND được đánh giá là cao và hấp dẫn, tạo động lực cho người chơi tham gia.
Game bài BETVND
Game bài là một trong những danh mục nổi bật tại BETVND, bao gồm các trò chơi bài truyền thống như Tiến lên, Phỏm, Xì tố, Bài cào, và Mậu binh. Game BETVND cung cấp các bàn chơi với nhiều mức cược khác nhau, từ nhỏ đến lớn, phù hợp với mọi đối tượng người chơi. Các trò chơi bài tại BETVND không chỉ mang tính giải trí cao mà còn đòi hỏi kỹ năng và chiến thuật tốt để giành chiến thắng.
Hướng dẫn cách tham gia nhà cái BETVND đơn giản
Tham gia cá cược tại nhà cái BETVND rất đơn giản và dễ dàng. Người chơi chỉ cần thực hiện một vài bước cơ bản dưới đây để bắt đầu:
Đăng ký BETVND
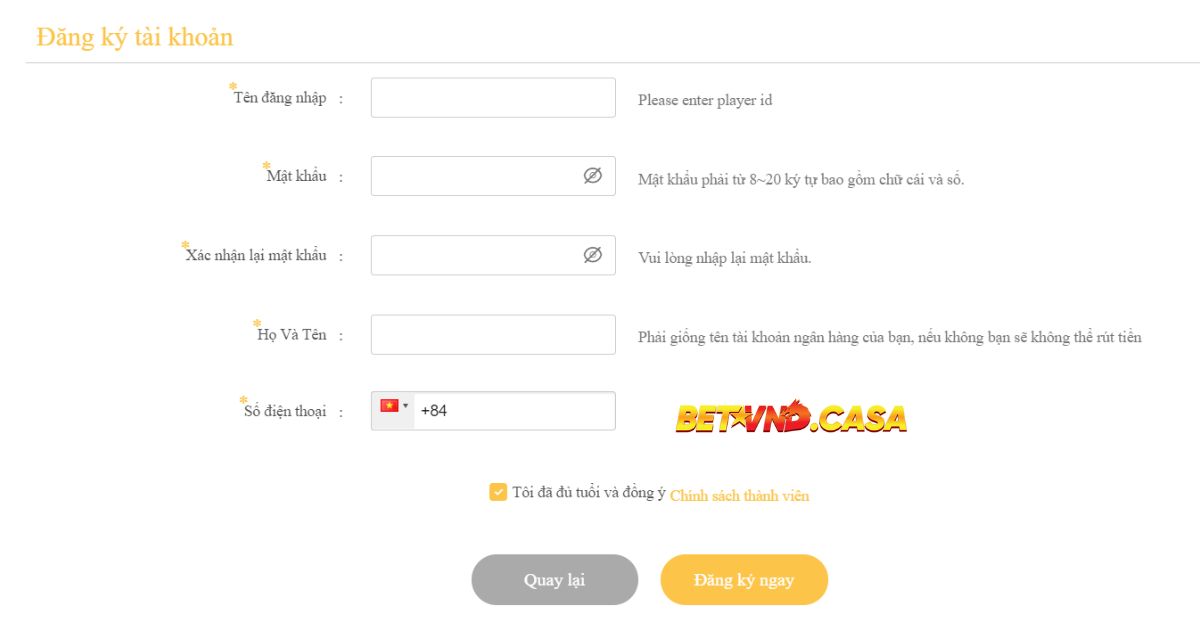
Truy cập vào trang web chính thức của BETVND: Truy cập vào trang web https://wingsforgreyhounds.org/ để bắt đầu quá trình đăng ký.
Nhấp vào nút “Đăng ký”: Nút này thường được đặt ở góc trên cùng bên phải của trang chủ.
Nhập thông tin cá nhân: Cung cấp đầy đủ và chính xác các thông tin như tên, email, số điện thoại và mật khẩu để tránh gặp phải sự cố khi sử dụng dịch vụ.
Xác nhận thông tin: Rà soát lại các thông tin đã nhập và nhấp vào nút “Đăng ký” để hoàn tất quá trình đăng ký.
Kích hoạt tài khoản: Kiểm tra hộp thư email để nhận liên kết kích hoạt từ nhà cái BETVND. Nhấp vào liên kết đó để kích hoạt tài khoản và bắt đầu sử dụng dịch vụ.
Đăng nhập nhà cái BETVND
Truy cập lại trang chủ BETVND: Sau khi đăng ký thành công, quay lại trang chủ BETVND.
Nhấp vào nút “Đăng nhập”: Nút này cũng nằm ở góc trên cùng bên phải của trang.

Nhập tên đăng nhập và mật khẩu: Sử dụng thông tin đã đăng ký để đăng nhập vào tài khoản.
Nhấp “Đăng nhập”: Nhấp vào nút “Đăng nhập” để truy cập tài khoản và bắt đầu tham gia cá cược.
Cách Nạp và Rút Tiền Tại BETVND
- Nạp Tiền: Đăng nhập vào tài khoản, chọn “Nạp tiền” và chọn phương thức nạp tiền phù hợp (chuyển khoản ngân hàng, ví điện tử, thẻ cào, v.v.). Điền thông tin và số tiền cần nạp, sau đó xác nhận giao dịch.
- Rút Tiền: Chọn “Rút tiền” từ tài khoản, điền thông tin tài khoản ngân hàng và số tiền muốn rút. Sau khi xác nhận, tiền sẽ được chuyển về tài khoản ngân hàng của người chơi trong thời gian ngắn.
Nhà Cái BETVND có những chương trình khuyến mãi gì?

Nhà Cái BETVND luôn có những chương trình khuyến mãi hấp dẫn dành cho cả người chơi mới và người chơi cũ. Những khuyến mãi nổi bật tại nhà cái BETVND gồm:
- Khuyến mãi đặc biệt: Các ưu đãi chào mừng dành cho người chơi mới, bao gồm tiền thưởng dành cho người chơi mới khi đăng ký tài khoản và thực hiện giao dịch nạp tiền lần đầu.
- Khuyến Mãi Nạp Tiền: Thưởng thêm phần trăm tiền nạp vào tài khoản trong các dịp đặc biệt.
- Hoàn Trả Cược Thua: Hoàn lại một phần tiền cược nếu người chơi thua lỗ trong một khoảng thời gian nhất định.
- Khuyến Mãi Giới Thiệu Bạn Bè: Thưởng tiền hoặc ưu đãi đặc biệt khi giới thiệu bạn bè tham gia BETVND.
Các Nền Tảng Có Thể Tham Gia Trò Chơi BETVND Gồm?
BETVND là một nền tảng cá cược trực tuyến đa dạng và linh hoạt, cho phép người chơi truy cập từ nhiều loại thiết bị khác nhau. Để đáp ứng nhu cầu của người chơi, BETVND hỗ trợ cả trên trình duyệt web và ứng dụng di động, mang lại trải nghiệm tối ưu và tiện lợi nhất.
Tham Gia Trò Chơi BETVND Trên Website

Người chơi có thể truy cập và tham gia trò chơi BETVND trực tiếp thông qua trình duyệt web trên máy tính bàn, laptop, hoặc thậm chí là trình duyệt trên thiết bị di động. Giao diện website của BETVND được thiết kế đơn giản, dễ sử dụng, nhưng vẫn đầy đủ các tính năng cần thiết cho một nền tảng cá cược chuyên nghiệp.
- Trải nghiệm trực quan: Trang web của nhà cái BETVND được tối ưu hóa cho màn hình lớn, giúp người chơi dễ dàng theo dõi các trận đấu trực tiếp, đặt cược, và thực hiện các thao tác nạp/rút tiền. Thông tin về các trận đấu, kèo cược, và kết quả đều được hiển thị rõ ràng và chi tiết.
- Khả năng tương thích cao: Trang web BETVND hoạt động mượt mà trên tất cả các trình duyệt phổ biến như Chrome, Firefox, Safari, và Edge, đảm bảo rằng người chơi có thể truy cập bất kỳ lúc nào, từ bất kỳ thiết bị nào.
- Bảo mật cao: BETVND chú trọng đến vấn đề bảo mật thông tin khách hàng. Với việc sử dụng các giao thức mã hóa SSL hiện đại, mọi thông tin cá nhân và giao dịch của người chơi đều được bảo vệ an toàn.
Tải BETVND Về Điện Thoại Di Động
BETVND hiểu rằng sự tiện lợi là yếu tố quan trọng đối với người chơi, vì vậy nền tảng này đã phát triển ứng dụng di động riêng cho cả hai hệ điều hành phổ biến là Android và iOS.
-
Cách tải ứng dụng BETVND:
Trên Android: Người chơi có thể tải app Betvnd trực tiếp từ trang web chính thức của BETVND bằng cách chọn phiên bản Android và làm theo hướng dẫn cài đặt. Vì lý do bảo mật, ứng dụng BETVND không có trên Google Play Store, nhưng các bước tải về và cài đặt đều đơn giản và an toàn.
Trên iOS: Người chơi có thể tải app Betvnd về thiết bị IOS thông qua App Store hoặc từ trang web chính thức của BETVND. Quá trình cài đặt dễ dàng, không yêu cầu người chơi thay đổi bất kỳ cài đặt bảo mật nào trên thiết bị.
-
Các điểm mạnh của ứng dụng di động:
Truy cập nhanh chóng và dễ dàng: App BETVND được thiết kế để hoạt động mượt mà trên tất cả các thiết bị di động, từ điện thoại thông minh đến máy tính bảng, giúp người chơi dễ dàng tham gia cá cược mọi lúc, mọi nơi với tốc độ và tiện lợi vượt trội so với trình duyệt web.
Thông báo đẩy: Ứng dụng cung cấp tính năng thông báo đẩy giúp người chơi không bỏ lỡ các sự kiện quan trọng, các trận đấu lớn, hoặc các chương trình khuyến mãi hấp dẫn.
Giao diện thu hút, dễ sử dụng: Với thiết kế giao diện đơn giản, tối ưu cho màn hình nhỏ, ứng dụng giúp người chơi dễ dàng thao tác và trải nghiệm mà không gặp bất kỳ khó khăn nào.
Những Câu Hỏi Mà Người Chơi Thắc Mắc Tại BETVND
Khi tham gia BETVND, người chơi thường có một số câu hỏi khó liên quan đến quy trình, bảo mật, và các chính sách của nền tảng. Dưới đây là những câu hỏi phổ biến và chi tiết giải đáp:

Lý Do Tài Khoản Bị Khóa Và Cách Mở Khóa?
Một số người chơi có thể gặp phải tình trạng tài khoản bị khóa vì nhiều lý do khác nhau, như vi phạm điều khoản sử dụng, đăng nhập sai nhiều lần, hoặc nghi ngờ có dấu hiệu gian lận. Để mở khóa tài khoản bạn cần làm theo các bước sau:
- Liên hệ với bộ phận hỗ trợ khách hàng của BETVND qua email hoặc chat trực tiếp trên trang web.
- Cung cấp thông tin cá nhân và các bằng chứng cần thiết để xác minh danh tính.
- Thực hiện theo hướng dẫn của nhân viên hỗ trợ để mở khóa tài khoản.
BETVND Có An Toàn Và Uy Tín Không?
Đây là câu hỏi quan trọng nhất mà nhiều người chơi mới đặt ra. BETVND được cấp phép và quản lý bởi các cơ quan uy tín trong ngành công nghiệp cá cược trực tuyến, đảm bảo rằng mọi hoạt động trên nền tảng này đều tuân thủ quy định và được kiểm soát chặt chẽ.
- Nền tảng áp dụng công nghệ mã hóa SSL để đảm bảo an toàn cho thông tin cá nhân và tài chính của người chơi.
- Các giao dịch nạp và rút tiền đều được thực hiện thông qua các phương thức an toàn, nhanh chóng, và minh bạch.
Thời Gian Xử Lý Đối Với Giao Dịch Nạp Và Rút Tiền Là Bao Lâu?
Thời gian xử lý nạp tiền tại BETVND thường rất nhanh, chỉ trong vài phút đối với hầu hết các phương thức. Tuy nhiên, rút tiền có thể mất từ 15 phút đến vài giờ tùy thuộc vào phương thức và ngân hàng liên kết. Người chơi cần chú ý cung cấp thông tin tài khoản ngân hàng chính xác để tránh tình trạng chậm trễ.
Làm Thế Nào Để Đảm Bảo Rằng Tôi Không Vi Phạm Quy Định Của BETVND?
Để tránh vi phạm quy định của BETVND, người chơi cần đọc kỹ và tuân thủ các điều khoản và điều kiện sử dụng dịch vụ của nền tảng. Một số điều mà bạn cần nhớ:
- Không tạo nhiều tài khoản dưới một tên người dùng hoặc địa chỉ IP.
- Không sử dụng các phần mềm, công cụ hoặc thủ thuật không hợp lệ để can thiệp vào trò chơi hoặc hệ thống.
- Tuân thủ các yêu cầu về thông tin cá nhân và tài khoản khi tham gia.
Kết luận
BETVND là một nền tảng cá cược trực tuyến uy tín và chất lượng tại Việt Nam, mang đến cho người chơi một trải nghiệm toàn diện với hàng loạt trò chơi đa dạng và hấp dẫn. Từ các trò chơi truyền thống như đá gà, tài xỉu, xổ số, lô đề, đến các trò chơi hiện đại như bắn cá và game bài, BETVND đều cung cấp những lựa chọn phù hợp cho mọi đối tượng người chơi.